OAuth 2.0 is the industry-standard authorization framework used to securely grant third-party applications access to user data without exposing login credentials. From social logins and enterprise single sign-on (SSO) to API security and cloud integrations, OAuth 2.0 underpins most modern authentication and authorization systems on the internet.
This article provides a clear, professional, and SEO-optimized explanation of OAuth 2.0, how it works, why it matters, and where it is used.
What Is OAuth 2.0?
OAuth 2.0 is an authorization protocol that allows applications to request limited access to a user’s protected resources hosted on another service. Instead of sharing usernames and passwords, OAuth 2.0 uses access tokens to delegate permissions securely.
In simple terms, OAuth 2.0 answers the question:
“What is this application allowed to do on behalf of the user?”
Why OAuth 2.0 Is Important for Security
Before OAuth, applications commonly required full account credentials to access user data. This approach introduced significant risks, including credential theft, over-privileged access, and poor revocation control.
OAuth 2.0 improves security by:
- Eliminating password sharing
- Enforcing least-privilege access using scopes
- Allowing token expiration and revocation
- Supporting secure third-party API access
- Enabling compliance with modern security standards
As a result, OAuth 2.0 has become the backbone of API security, cloud authentication, and enterprise identity management.
OAuth 2.0 vs Authentication (Key Difference)
A common misconception is that OAuth 2.0 is an authentication mechanism.
- Authentication verifies user identity (who the user is)
- Authorization defines permissions (what access is granted)
OAuth 2.0 handles authorization only. When authentication is required, OAuth 2.0 is typically combined with OpenID Connect (OIDC), which adds an identity layer on top of OAuth.
Core Components of OAuth 2.0
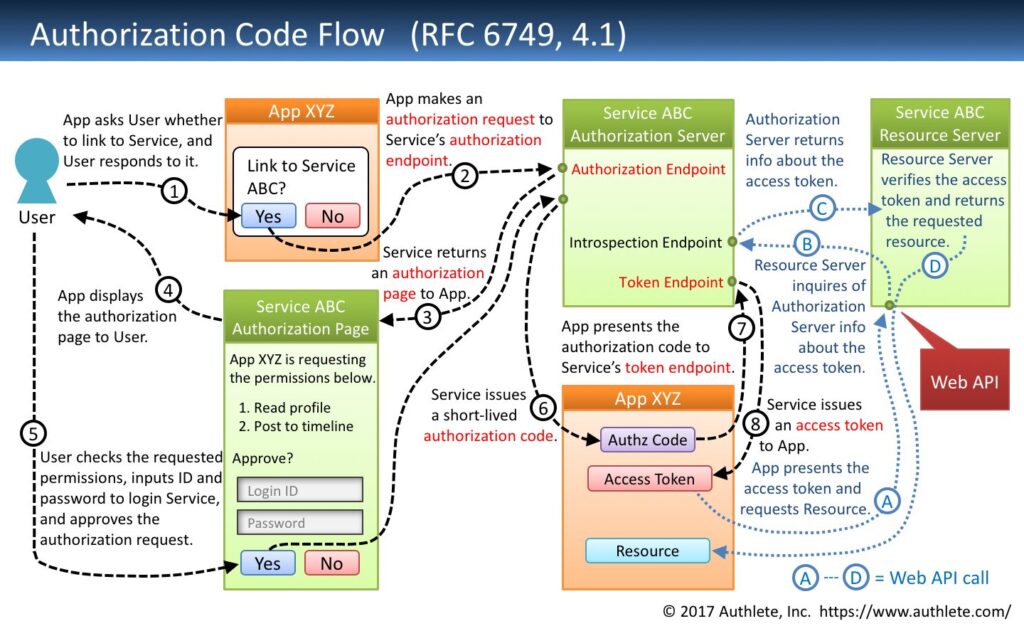
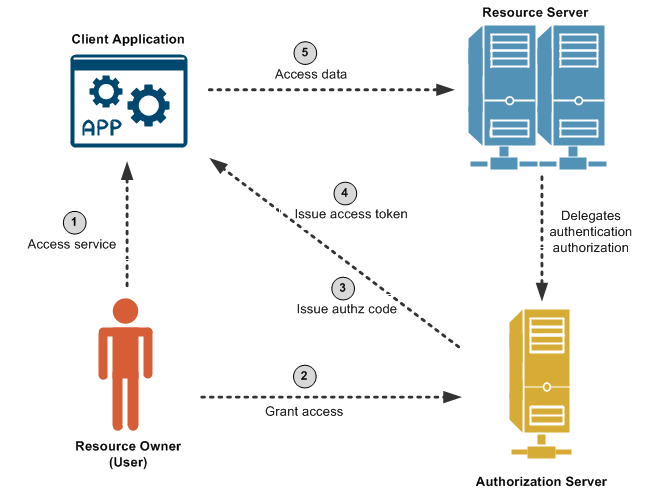
OAuth 2.0 defines four primary roles:
1. Resource Owner
The end user who owns the protected data.
2. Client Application
The application requesting access to the user’s resources.
3. Authorization Server
The server that authenticates the user and issues tokens.
4. Resource Server
The API that stores and serves protected data.
This separation of responsibilities is central to OAuth 2.0’s secure architecture.
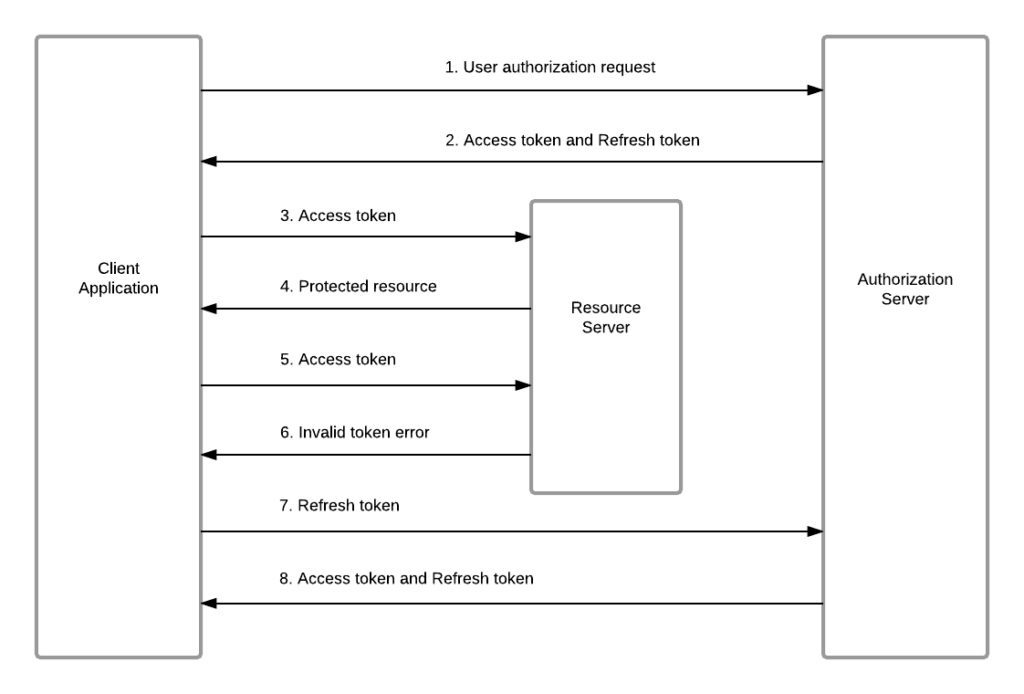
OAuth 2.0 Tokens Explained
Tokens are the foundation of OAuth-based authorization.
Access Token
- Short-lived credential
- Sent with each API request
- Represents granted permissions (scopes)
Refresh Token
- Long-lived credential
- Used to obtain new access tokens
- Never shared with APIs
Tokens may be opaque strings or JSON Web Tokens (JWTs), depending on the implementation.
OAuth 2.0 Scopes and User Consent
Scopes define what actions an application can perform. They provide granular permission control and transparency for users.
Common examples include:
read:profileemailcalendar.readpayments.write
Users explicitly approve requested scopes during the consent process, ensuring controlled and auditable access.
OAuth 2.0 Grant Types (Authorization Flows)
OAuth 2.0 supports multiple grant types to accommodate different application architectures.
Authorization Code Grant
The most secure and recommended OAuth flow. Used by web applications, mobile apps, and SPAs. Tokens are exchanged server-side, reducing exposure.
Authorization Code with PKCE
A security-enhanced version of the Authorization Code flow. Mandatory for public clients such as single-page applications and mobile apps.
Client Credentials Grant
Used for machine-to-machine authentication, where no user is involved. Common in microservices and backend API communication.
Device Authorization Grant
Designed for devices with limited input, such as smart TVs, consoles, and IoT devices.
Deprecated flows like the Implicit Grant are no longer recommended due to security vulnerabilities.
Common OAuth 2.0 Use Cases
OAuth 2.0 is widely used across industries and platforms, including:
- Social login (Google, Microsoft, GitHub)
- Enterprise SSO and identity federation
- API authorization and access control
- Cloud services and SaaS platforms
- Mobile and SPA authentication flows
- Microservices and zero-trust architectures
Is OAuth 2.0 secure?
Yes. When implemented correctly using modern best practices (HTTPS, PKCE, short-lived tokens), OAuth 2.0 is highly secure.
Does OAuth 2.0 replace passwords?
No. OAuth eliminates password sharing with third-party apps, but users still authenticate with the authorization server.
Is OAuth 2.0 authentication or authorization?
OAuth 2.0 is an authorization framework. Authentication is handled separately or via OpenID Connect.
Conclusion
OAuth 2.0 is a foundational technology for secure, scalable, and user-centric access control in modern applications. By replacing credential sharing with token-based authorization, it enables safer integrations, better user trust, and robust API security.
Whether you are building APIs, SaaS platforms, mobile applications, or enterprise systems, understanding OAuth 2.0 is essential for designing secure and future-proof architectures.
If you would like this article adapted for:
- Technical documentation
- Blog publishing (Medium, Dev.to)
- Enterprise whitepapers
- Developer onboarding guides